A network security breach is a potentially painful and costly issue to manage, not to mention the potential impact on your business’ reputation if your logo becomes associated with theft of your clients’ personal information.
Here’s a case that illustrates the point: Remember Mossack Fonseca, the company that was at the center of the Panama Papers leak in 2016? They shut their doors in 2018 – now their domain name is owned by a British company spruiking its ability to get struck off companies registered again. The breach literally killed the company.
These days there are a huge number of technology solutions for security, but unfortunately, humans still use computers and they remain one of the weakest links in the security chain. If you’re not already conducting security awareness training for your team, here’s why you should.
But first…
What is security awareness training?
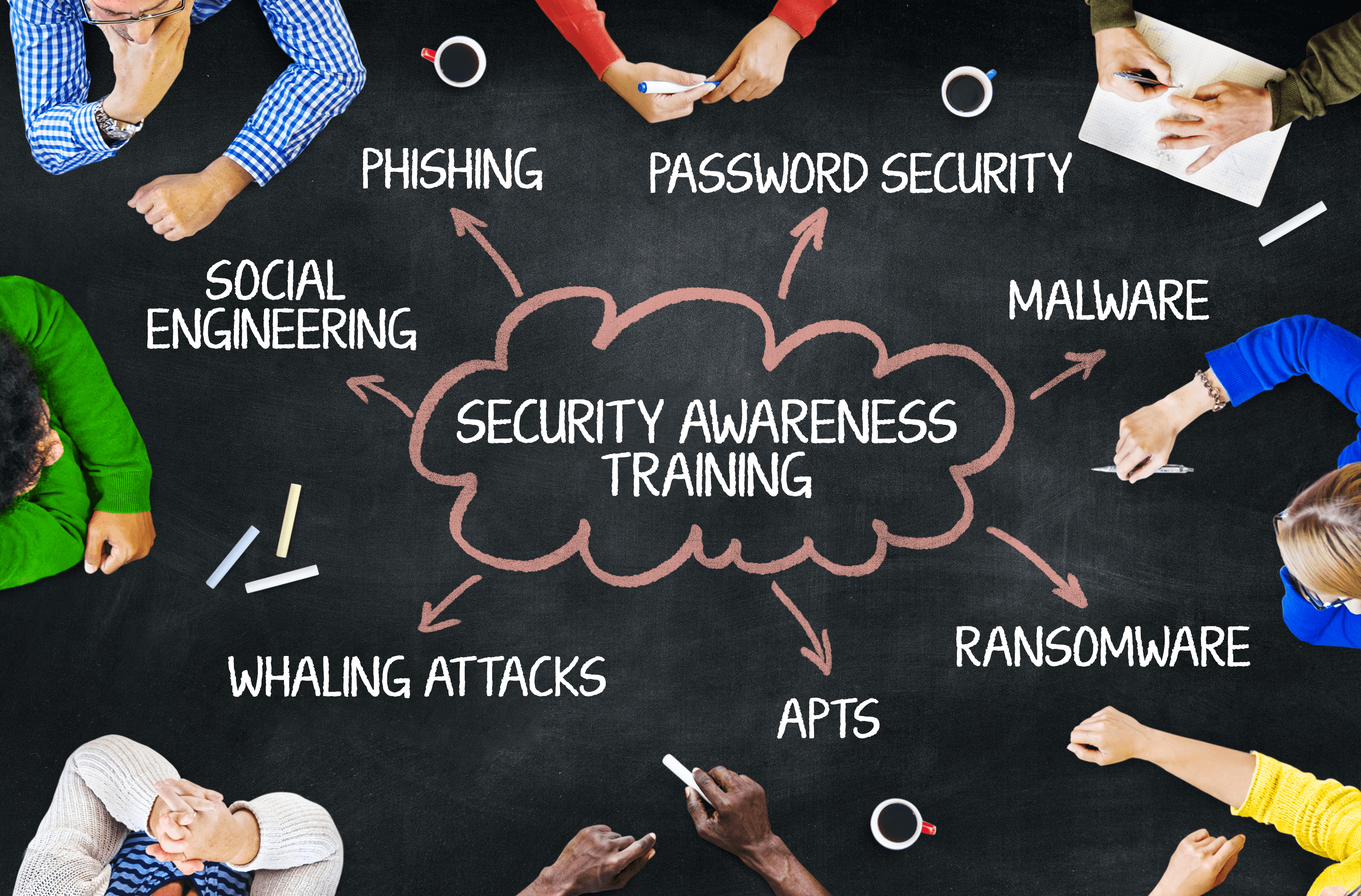
Security awareness training is an education program that aims to educate and assist employees in comprehending their security obligations and how their actions can influence risk. The content and delivery method of security training will vary depending on the goals of your organization and the existing knowledge of those being trained.
Why is security awareness training important?
It should come as no surprise that organizations are placing a higher value on cyber security as the scale of threats increases and attack vectors multiply. But technology alone is not enough to address the problem. It is critical that your staff are educated to spot danger and report on potential issues as part of your overall “security fabric”. While phishing emails are a favourite approach for compromising your business, there are numerous other types of attack vector that can lead to a breach. To obtain the most effective protection, it’s important to build a security awareness culture from top to bottom in your organization.
Does security awareness training work?
Yes, it does. But, like any form of training, the effects diminish over time. A single training course will increase your team’s perception of danger and their propensity to take the correct action for a while, but inevitably many of the learnings will be forgotten and your team dynamics will change – current team members will leave and new staff will replace those that have undertaken the training.
Developing a continuous cycle of training, on new and improved threats and attackers’ techniques for avoidance, will deliver the largest cumulative benefit.
What does cyber security training look like?
Every organization has a different attack surface and while, say, 90% of training will suit every business, there will undoubtedly be specific threats that are unique to your organization.
The most effective form of training is one that has been custom-designed for your organization based on an arms-length assessment of the people on your team, the processes they execute, the resources they access and your geographic spread as a team among other factors. The type of organization you run, plus the level of prior training your team has consumed will also play a role in determining the best approach.
Common training items will look like this: checking the legitimacy of emails, the consequences of data leakage, how to securely send and receive files and the processes for securely offboarding exiting team members.
What are the most common risks addressed by cyber security training?
Every organization’s risk profile is different, but some common themes apply. Poor practices regarding payment authorizations, insufficient protocols around the security of passwords, inattention to email security indicators and failure to enforce policy restrictions on USB devices are just some of the most common problems that we can address.
How do you know if cyber security training is working?
This is probably the biggest bugbear for any IT training program manager – the training is most effective when attacks are unsuccessful and thus, don’t cause a fuss in the organization. Conversely, this makes further expenditure on training seem less necessary, because cybersecurity threats are being handled. Thus, tracking the number of near misses becomes an important tool for justifying ongoing investment.
What should an ongoing training program look like?
An in-person or video-based training primer and refresher combination should be conducted at least every 12 months. Six months is ideal, as your staff can be brought up to speed with the latest security threat indicators and yet it’s not so often that the training seems too repetitive. The difference between computers and humans is that a computer will follow the same procedure a million times without cutting corners. Humans need frequent repetition of message and reinforcement of managerial expectations to achieve the same level of conformance.
In between in-person training, we recommend a quarterly cycle of training refreshers be delivered by email to your users. Tracking those that complete the short quizzes and reading assignments can be conducted, so you can identify staff at greater risk of compromise.
Leave a Reply